Reading time: 7 minutes / Become my affiliate / Sponsor this newsletter
Greetings from above,
Why do vibe coders sleep so well at night?
Because their API keys sleep right there in the codebase with them.
Last year, a friend shipped a SaaS in a weekend using Claude. Full product. Working payments. Live URL. He was proud.
Three days later, someone had scraped his exposed API keys from the public GitHub repo, racked up $4,200 in OpenAI bills, and his app was serving responses to random bots worldwide.
He hadn't touched auth. Hadn't set session limits. Hadn't sanitized a single input. The AI wrote the code. He just hit deploy.
That's vibe coding. It's fast. It's fun. And it will absolutely get you wrecked in production if you skip the security layer.
Today's newsletter will show you:
The 5 security categories every vibe coder ignores before shipping
The 24 rules that actually matter (from auth to webhooks)
One mega-prompt to audit your entire codebase before it goes live
Let's build your competitive advantage!
AI Agents Are Reading Your Docs. Are You Ready?
Last month, 48% of visitors to documentation sites across Mintlify were AI agents—not humans.
Claude Code, Cursor, and other coding agents are becoming the actual customers reading your docs. And they read everything.
This changes what good documentation means. Humans skim and forgive gaps. Agents methodically check every endpoint, read every guide, and compare you against alternatives with zero fatigue.
Your docs aren't just helping users anymore—they're your product's first interview with the machines deciding whether to recommend you.
That means:
→ Clear schema markup so agents can parse your content
→ Real benchmarks, not marketing fluff
→ Open endpoints agents can actually test
→ Honest comparisons that emphasize strengths without hype
In the agentic world, documentation becomes 10x more important. Companies that make their products machine-understandable will win distribution through AI.
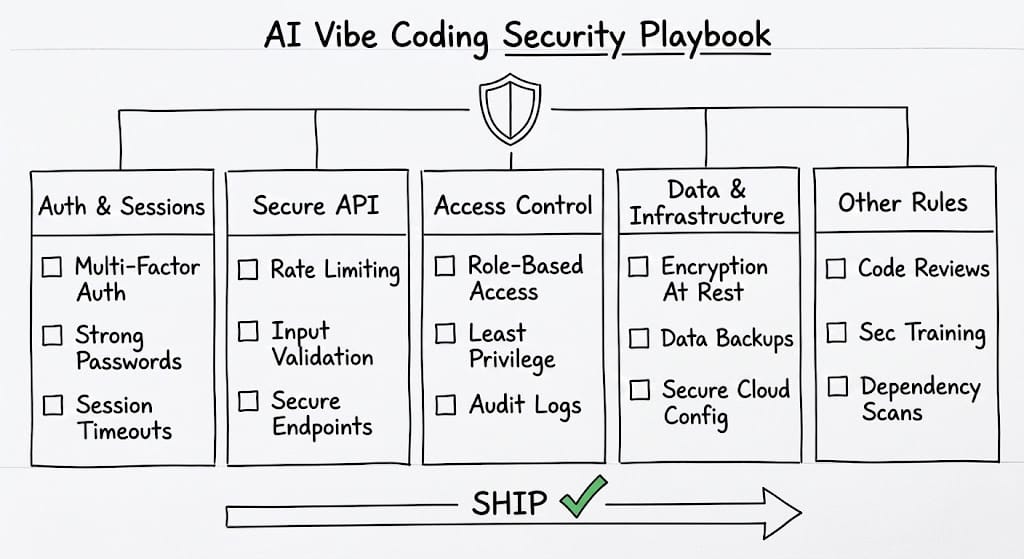
🎯 THE VIBE CODING SECURITY PLAYBOOK 🎯
AI lets you ship in hours. But shipping fast without a security checklist is like sprinting through a minefield in flip-flops.
The 24 rules below are the ones professionals check before every production deploy. Most vibe coders skip all of them.
🔐 Category 1: Authentication & Sessions 🔐
This is where most breaches start. Weak sessions, AI-generated auth, and exposed keys are the trifecta of getting owned.
Rule 01 - Session Lifetime. Set session expiration limits. JWT sessions should never exceed 7 days and must use refresh token rotation.
Rule 02 - No AI-built auth. Never use AI-generated authentication flows. Use Clerk, Supabase, or Auth0. These libraries have been battle-tested. Your AI-written session handler hasn't.
Rule 03 - API key security. Due to chat access, keep API keys strictly secured. Use process.env keys. Never hardcode them. Never commit them. Never log them.
The "why" here is simple. AI is great at scaffolding logic. It's terrible at security edge cases. Auth has too many attack vectors for a first-draft implementation to handle safely.
🔧 Category 2: Secure API Development
You built the API. Now someone's going to try to break it. These five rules dramatically shrink your attack surface.
Rule 04 - Rotate secrets every 90 days minimum. Set a calendar reminder. Do it.
Rule 05 - AI package verification. Have the AI verify all suggested packages for security before installing. Ask it to check for known vulnerabilities before you npm install anything.
Rule 06 - Prefer newer package versions. Always opt for newer, more secure package versions. Old packages have documented CVEs. New ones are harder to exploit.
Rule 07 - Run npm audit fix after every build. Not sometimes. Every build. Automate it in your CI pipeline if you can.
Rule 08 - Sanitize all inputs using parameterized queries always. SQL injection is still the #1 attack vector. Parameterized queries eliminate it entirely.
🚧 Category 3: API & Access Control 🚧
You don't just need to secure what's inside your API. You need to control who gets access to it, from where, and how often.
Rule 09 - Enable Row-Level Security in your DB from day one. Don't add it later. It's 100x harder to retrofit. Supabase makes this easy.
Rule 10 - Remove all console.log statements before deploying to production. Logs leak data. Logs expose logic. Strip them.
Rule 11 - Use CORS to restrict access to your allow-listed production domain. Open CORS is an open door.
Rule 12 - Validate all redirect URLs against an allow-list. Open redirects let attackers phish using your trusted domain.
Rule 13 - Add auth and rate limiting to every endpoint. No exceptions. Even internal endpoints. Rate limiting stops brute force and abuse.
🏗️ Category 4: Data & Infrastructure 🏗️
Where you store data, how you handle uploads, and how you process payments. Each one is a potential exploit if not handled right.
Rule 14 - Cap AI API costs within your code and dashboard. Set hard spending limits. Attackers love running up your AI bills.
Rule 15 - Add DDoS protection via Cloudflare or Vercel edge config. This takes 10 minutes and protects you from the most common infrastructure attack.
Rule 16 - Lock down storage access so users can only access their own files. Insecure direct object references are one of the OWASP Top 10.
Rule 17 - Validate upload limits by signature, not by extension. File extension checks are trivially bypassed. Check file signatures (magic bytes) instead.
Rule 18 - Verify webhook signatures before processing payment data. Stripe, Lemon Squeezy, all of them send signatures. Use them. Or anyone can fake a payment event to your endpoint.
📋 Category 5: Other Rules That Actually Matter 📋
These six rules cover the edge cases that only become obvious after something goes wrong.
Rule 19 - Server-side UI-level checks are not security. Hiding a button in the UI doesn't protect the endpoint. Always enforce permissions server-side.
Rule 20 - Log critical actions: deletions, role changes, exports. You need an audit trail when something bad happens.
Rule 21 - Build real account deletion flows. Large fines are not fun. GDPR requires actual deletion. Soft deletes don't count legally.
Rule 22 - Automate backups then actually test them. An untested backup is useless. Schedule a monthly restore test.
Rule 23 - Keep test and production environments fully separate. Prod data in test environments is how leaks happen.
Rule 24 - Never let webhooks touch real systems in the test environment. Test webhooks should hit test endpoints. Period.
⚙️ THE PROMPT: Vibe Code Security Auditor ⚙️
This mega-prompt turns Claude into your production security reviewer. Paste your codebase (or key files) and it will audit all 24 rules, flag every violation, and give you a prioritized fix list before you ship.
What you'll get:
A pass/fail check against all 24 rules with specific line references
Severity ratings for every issue found (Critical / High / Medium / Low)
Ready-to-implement code fixes for each violation
An estimated time to fix each issue
💡 Paste your code + this prompt before every production deploy.
<role>
You are a senior security engineer specializing in full-stack web application security.
You have deep expertise in authentication systems, API security, infrastructure hardening,
and OWASP best practices. Your job is to audit code before it ships to production.
</role>
<context>
I am a developer preparing to deploy a web application to production. I am going to paste my codebase (or key files) below. I need you to run a comprehensive security audit against the 24 rules in the AI Vibe Coding Security Playbook before I ship.
</context>
<security_rules>
AUTHENTICATION & SESSIONS:
01. Session lifetime: JWT sessions must not exceed 7 days; refresh token rotation required
02. No AI-built auth: Must use Clerk, Supabase, or Auth0 - not custom implementations
03. API keys must use process.env - never hardcoded, logged, or committed
SECURE API DEVELOPMENT:
04. Secrets must be rotated every 90 days minimum (check for rotation policy in code)
05. All npm packages must be verified for known vulnerabilities before install
06. Package versions must be current and secure (no pinned outdated versions)
07. npm audit fix must run after every build (check for CI/CD pipeline)
08. All inputs must use parameterized queries - no raw SQL string concatenation
API & ACCESS CONTROL:
09. Row-Level Security must be enabled on database from day one
10. No console.log statements in production code
11. CORS must restrict access to allow-listed production domains only
12. All redirect URLs must be validated against an allow-list
13. Every endpoint must have auth AND rate limiting - no exceptions
DATA & INFRASTRUCTURE:
14. AI API costs must be capped in code and dashboard
15. DDoS protection must be configured via Cloudflare or Vercel edge
16. Storage access must be scoped to the authenticated user only
17. File uploads must validate by signature (magic bytes), not file extension
18. Webhook signatures must be verified before processing payment data
OTHER CRITICAL RULES:
19. All security checks must be enforced server-side, not just in UI
20. Critical actions (deletions, role changes, exports) must be logged
21. Account deletion must permanently delete data (GDPR-compliant, not soft delete)
22. Backup automation with tested restore procedures must exist
23. Test and production environments must be fully separated
24. Webhooks must never touch real systems in test environments
</security_rules>
<instructions>
Step 1: Read every file I paste below carefully.
Step 2: For each of the 24 rules above, determine:
- PASS: Rule is clearly implemented correctly
- FAIL: Rule is violated (provide exact file name and line number)
- NOT FOUND: Cannot determine from code provided (flag for manual review)
Step 3: For every FAIL, provide:
- Severity: CRITICAL / HIGH / MEDIUM / LOW
- What the violation is (plain English, one sentence)
- The specific code that is wrong (quote it)
- The exact fix with working code replacement
- Estimated time to fix
Step 4: Produce a PRODUCTION READINESS SCORE:
- Count: X/24 rules passing
- List all CRITICAL and HIGH severity issues at the top
- State clearly: SHIP or DO NOT SHIP with reasoning
Step 5: Provide a PRIORITIZED FIX LIST ordered by:
1. CRITICAL severity first
2. Time to fix (quickest wins first within same severity)
3. Include a realistic total fix time estimate
Format your output with clear headers for each section.
Be specific. Reference exact lines. Never give vague advice.
If something is missing from the code I provide, flag it clearly
and tell me exactly what to check manually.
</instructions>
<code_to_audit>
[PASTE YOUR CODEBASE OR KEY FILES HERE]
</code_to_audit>Customize these variables before using:
[PASTE YOUR CODEBASE OR KEY FILES HERE]: Paste your full project, or prioritize: auth files, API routes, database queries, payment handlers, and environment config.
Pro tips:
Run this on every file that touches auth, payments, or user data first.
If your codebase is large, audit by category: paste auth files first, then API routes, then DB queries.
Save the output as your pre-deploy security checklist. Run it again after any major feature addition.
📋 Summary 📋
Vibe coding ships fast. Production security requires 24 specific checks across 5 categories.
The biggest risks: hardcoded API keys, no auth on endpoints, missing input sanitization, and skipped webhook verification.
The Security Auditor prompt above catches violations in minutes and gives you working code fixes with severity ratings.
📚 FREE RESOURCES 📚
📦 WRAP UP 📦
What you learned today:
The 5 Security Categories - Auth & Sessions, Secure API Development, Access Control, Data & Infrastructure, and the edge-case rules that catch you off-guard.
24 Rules That Actually Matter - not theoretical, not generic. Specific, numbered, production-ready checks.
The Security Auditor Prompt - paste your code, get a SHIP or DO NOT SHIP verdict with a prioritized fix list.
No more shipping blind and hoping for the best.
You now have a structured system to audit your AI-built apps before they go live.
What did you think about today's edition?
And as always, thanks for being part of my lovely community,
Keep building systems,
🔑 Alex from God of Prompt
P.S. What are you building with AI right now that needs this audit most? A SaaS, an internal tool, or a client project? Reply and I'll tailor the next newsletter to your use case.